An Introduction to Virtual Private Network ( VPN) :-
An Introduction to Virtual Private Network ( VPN) :-
A virtual private network (VPN) in the most generic sense refers to a private network connection that is overlaid onto a public network.
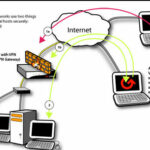
A Virtual Private Network (VPN) allows you to connect branch offices, telecommuting workers, field representatives and other users into one seamless network. When referring to the Internet, the term VPN usually refers to overlaying a private network connection onto the Internet. Because the Internet is the most public data network available, it is important to secure communications between remote offices and users when using the Internet as the transport medium.
You can easily understand the concept of VPN with this Youtube video. 🙂
http://www.youtube.com/watch?feature=player_detailpage&v=IwJajHtegZI
By using VPN technology, you not only secure information, but you also emulate a private network link for each VPN connection. Because VPNs on the Internet operate over an IP network (Layer 3), these VPNs are referred to as Layer 3 VPNs.
The VPN provides the following benefits:-
• Privacy or confidentiality of the data :- The VPN uses encryption to guarantee that traffic between
the two offices is secret. An attacker that intercepts the traffic cannot understand it.
• Data integrity :- The VPN guarantees that the data that passes through it has not been altered in
transit.
• Data authentication :- The VPN guarantees that data that passes through the tunnel actually
comes from one of the two endpoints of the VPN,and not from some attacker on the Internet.
• Direct private IP address to private IP address communication :- The computers at the two offices
communicate as if they were not behind devices configured with Network Address Translation
(NAT). The data tunnels through NAT for a transparent connection between the devices.
How VPN Works :-
1. Authorization ensures that only trusted hosts can gain network access. If a computer has not logged in with the VPN gateway , the connection is denied (1a). if a computer provides authorization credentials such as a password and pre-shared secret, the VPN gateway adds the computer to its list of computers allowed to connect (1b).
2. Encryption defeats interception of traffic by scrambling data. Once authorized, a computer can use encryption to prevent digital eavesdropping (packet sniffing) by any in-between points on the Internet, including unauthorized hosts.
Note :- This tutorial is just for basic concept understanding. I will try to write more and more on VPN technologies in my future articles. 🙂
Also Check :-
An Introduction to IPSec Protocol
Nmap – Free Security Scanner For Network Exploration and Hacking
An introduction to information security
The OSI Model’s Seven Layers Defined and Functions Explained
What is a Web Application Firewall
What is Stateful Packet Inspection Firewall
Hope you like my post.An Introduction to Virtual Private Network ( VPN). Please Share with others.