How to Configure a WatchGuard Fireware XTM Device Interfaces :-
An XTM device has three types of interfaces: external, trusted, and optional. To use your device in a network, you must set the IP addresses of the interfaces.
A firewall physically separates the networks on your local area network (LAN) from those on a wide area network (WAN) like the Internet. One of the basic functions of a firewall is to move packets from one side of the firewall to the other. This is known as routing. To route packets correctly, the firewall must know what networks are accessible through each of its interfaces.
The device provides additional functionality for some interfaces. External interfaces can be configured to work with Dynamic DNS. Trusted and optional interfaces can be set up with the device as a DHCP (Dynamic Host Configuration Protocol) server.
External Interfaces :-
A device external interface connects to a wide area network (WAN), such as the Internet, and can have either a static or dynamic IP address. The device gets a dynamic IP address for the external interface from either a DHCP server or PPPoE (Point-to-Point Protocol over Ethernet) server.
Trusted Interfaces :-
A trusted interface connects the private local area network (LAN) or internal network that you want to secure. Because a trusted interface is a LAN interface, the IP address for a trusted interface is static. Usually, trusted interfaces use private or reserved IP addresses that conform to RFC 1918.
Optional Interfaces :-
Optional interfaces connect to your optional networks, which are mixed trust or DMZ environments separated from your trusted networks. Public web, FTP, and mail servers are usually found in optional networks.
Requirements for XTM Device Interfaces :-
Each interface on the XTM device can connect to a different network. The computers and servers protected by the device can use either private or public IP addresses. The device uses network address translation (NAT) to route traffic from the external network to computers on the trusted and optional networks.
All devices behind the trusted and optional interfaces must have an IP address from the network assigned to that interface. To make this easy to remember, many administrators set the interface address to the first or last IP address in the range used for that network.
In the below topology, We have to configure Eternal Interface IP-address ( 24.4.5.7/24 ) , Trusted Interfaces ( 10.10.10.254 ) and Optional Interface address 192.168.10.254
Before starting configuration, Your laptop must have WatchGuard System Manager ( WSM ) installed.
From the Windows desktop :-
1. Select Start > All Programs > WatchGuard System Manager 11.5.2
Navigate to File > Connect To Device. here you have to enter IP-address of your device. You can easily find out the interface IP-address on the Device panel. and in the Pass-phrase enter the ” readonly ”
On the Device Status tab, click the plus sign (+) to expand the device entry. Information about the device appears.
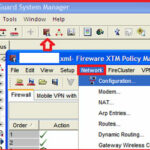
now Click on the Policy manager icon to open Fireware XTM policy manager. Click on the Network > Configuration.
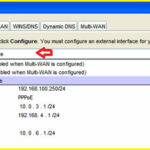
now here you have three mode for Interface configuration. Select the Mixed Routing mode and select your interface and click on the Configure option to configure your interfaces.
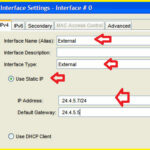
now here you have option to configure your IP-address. Static IP , Using DHCP and PPOE. In our case we have to use Static IP here. Enter Your Interface name and select the type External and enter your IP-address and gateway assigned by your ISP.
If you have more than one IP-address provided by ISP then you can add in the Secondary tab. Click on the Add and add your IP-addresses here.
now you have to configure your Trusted interface. Select the Trusted port and click on the Configure option and enter your name of interface and IP-address here.
Now you have to define NAT rule for interfaces. Navigate to XTMPolicy manager > Network > NAT.
Here in the Dynamic NAT option, add all your local inside address range that you want to give the access of internet.
Now in the 1 to 1 NAT, add your Internal server ip-address.
Now you have to save all these configurations on your Firbox XTM device.
After saving configurations, your all defined internal addresses are able to access internet. 🙂
Hope you like my post.How to Configure a WatchGuard Fireware XTM Device Interfaces. Please share with others.
Related Post :-
What is WatchGuard System Manager(WSM)
Stop Unwanted Email with SpamBlocker in WatchGuard