An Introduction to Ethernet Cabling :-
If you are looking for a carrier in Network Administration then it’s essentials for you to understand the Ethernet cabling. In Network, Your first step of troubleshooting is start on Physical layer. Because if your devices are not properly connected in correct order then there is no meaning of any troubleshooting. So it’s really important for you to understand the Ethernet cabling.
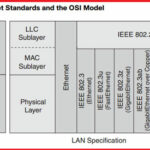
In the OSI model, Ethernet technology operates at the physical and data link layers – Layers One and Two respectively.
Traditional Ethernet supports data transfers at the rate of 10 Megabits per second (Mbps). Over time, as the performance needs of LANs have increased, the industry created additional Ethernet specifications for Fast Ethernet and Gigabit Ethernet. Fast Ethernet extends traditional Ethernet performance up to 100 Mbps and Gigabit Ethernet up to 1000 Mbps speeds. Although products aren’t yet abvailable to the average consumer, 10 Gigabit Ethernet (10000 Mbps) also remains an active area of research.
Ethernet has continued to evolve from the 10BASE2 flavor capable of speeds up to 185 Mbps to the newest 10GigE (10 Gigabit Ethernet) capable of speeds up to 10 Gbps. Since 1985, IEEE has continued to upgrade the 802.3 standards to provide faster speeds without changing the underlying frame structure.
802.3 is the IEEE standard for Ethernet, and both terms are commonly used interchangeably. The terms Ethernet and 802.3 both refer to a family of standards that together define the physical and data link layers of the definitive LAN technology.
Ethernet separates the functions of the data link layer into two distinct sublayers:-
- Logical Link Control (LLC) sublayer:- Defined in the 802.2 standard.
- Media Access Control (MAC) sublayer:- Defined in the 802.3 standard.
The LLC sublayer handles communication between the network layer and the MAC sublayer. In general, LLC provides a way to identify the protocol that is passed from the data link layer to the network layer. In this way, the fields of the MAC sublayer are not populated with protocol type information, as was the case in earlier Ethernet implementations.
The category 5 Enhanced UTP cable can handle speeds up to a gigabit with a distance of up to 100 meters. Typically we’d use this cable for 100 Mbps and category 6 for a gigabit, but the category 5 Enhanced is rated for gigabit speeds and category 6 is rated for 10 Gbps!
You need to really understand the following Three types of cables:-
- Straight-through cable
- Crossover cable
- Rolled cable
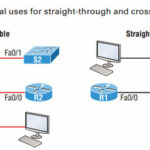
Straight-through cable :-
The straight-through cable is used to connect the following devices:-
- Host to switch or hub
- Router to switch or hub
Four wires are used in straight-through cable to connect Ethernet devices.
Crossover Cable :-
The crossover cable can be used to connect the following devices:-
- Switch to switch
- Hub to hub
- Host to host
- Hub to switch
- Router direct to host
- Router to router
Rolled Cable :-
Although rolled cable isn’t used to connect any Ethernet connections together, you can use a rolled Ethernet cable to connect a host EIA-TIA 232 interface to a router console serial communication (COM) port.
If you have a Cisco router or switch, you would use this cable to connect your PC, Mac, or a device like an iPad to the Cisco hardware.Eight wires are used in this cable to connect serial devices, although not all eight are used to send information, just as in Ethernet networking.
This post is going to be more theoretical. actually my main intention to write this article was to introduce Ethernet cabling concept to my readers. 🙂
Hope you like my post.An Introduction to Ethernet Cabling. please Share with others.
Also Check :-
Most Common Interview Questions on OSI model
The OSI Model’s Seven Layers Defined and Functions Explained
What is differences between TCP and UDP