Nmap – Free Security Scanner For Network Exploration and Hacking :-
Nmap – Free Security Scanner For Network Exploration and Hacking :-
Nmap (“Network Mapper”) is a free and open source (license) utility for network exploration or security auditing. Many systems and network administrators also find it useful for tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime.
Nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics. It was designed to rapidly scan large networks, but works fine against single hosts.
For Windows you need to be download, but for Linux it,s pre-installed. i am using nmap on Linux. you can easily find out the your ip-address with ipconfig command on the windows command prompt or ifconfig command on the Linux terminal. By defauly nmap is scanning 1000 ports by default.
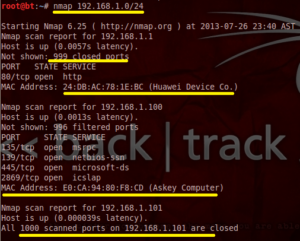
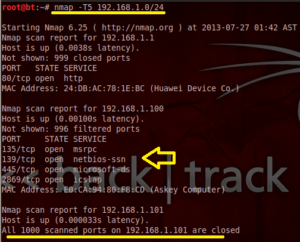
1. Find out all Open ports in a network
| root@bt:~# nmap 192.168.1.0/24 or root@bt:~# nmap 192.168.1.0-255 |
This command will show you all the opened ports on the given network , Mac-address of all the connected devices.
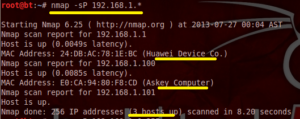
2. Find out Live Host :-
| root@bt:~# nmap -sP 192.168.1.* or root@bt:~# nmap -sP 192.168.1.0-255 |
This command will perform only ping scan to find out the live host in network including mac-address of devices. This command is not performing TCP or UDP scan.
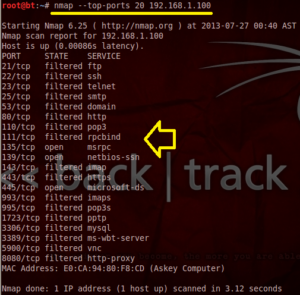
3. Scan Top Ports
By default nmap is scanning 1000 ports. but you have option to scan top ports only. where 20 is defining top 20 ports.
| root@bt:~# nmap –top-ports 20 192.168.1.10 or root@bt:~# nmap –top-ports 20 192.168.1.0/24 |
4. Find out Particular open Port
| root@bt:~# nmap –sT –p80 192.168.1.1-50 |
This command will help you to find out particular port only. In this syntex -sT is representing SYN request and -p is representing the protcol. 80 is port number of http.
5. Hide your Source IP-address during scan :-
| root@bt:~# nmap –sS 192.168.1.1-5 –D 192.168.1.98,192.168.1.99 |
Most of the time scan is easily going detected. so in this condition use -D syntex this will hide your real source IP-address and it will show you other IP-address defined after -D syntax.
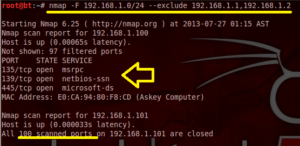
6. Scan Top 100 Ports and Exclude some IP-address
| root@bt:~# nmap -F 192.168.1.0/24 – -exclude 192.168.1.98,192.168.1.99 |
-F syntax will scan 100 ports with — exclude syntax you can easily exclude some IP-address.
7. Exclude ICMP in your Scan
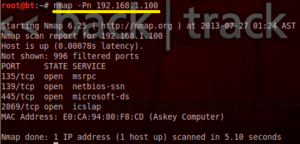
| root@bt:~# nmap –Pn 192.168.1.100 |
By default, nmap is doing first icmp scan but with the -Pn syntex you can exclude the icmp request during scan.
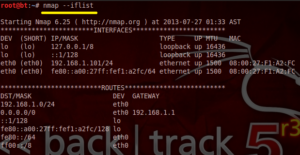
8. Find out Interface Info :-
| root@bt:~# nmap – -iflist |
With this command you can find out the all interface information including IP-address and gateway address.
| root@bt:~# nmap -T5 192.168.1.0/24 |
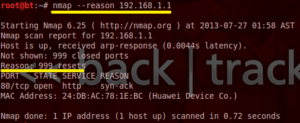
10. Display the reason a port is in Particular state
| root@bt:~# nmap –reason 192.168.1.1 |
Nmap Scripting Engine :-
The Nmap Scripting Engine (NSE) is one of Nmap’s most powerful and flexible features. It allows users to write (and share) simple scripts to automate a wide variety of networking tasks. Those scripts are then executed in parallel with the speed and efficiency you expect from Nmap.
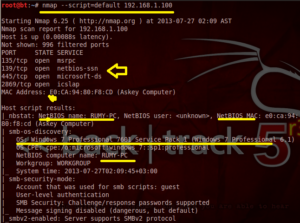
11. Default Scrpting Engine
| root@bt:~# nmap – -script=default 192.168.1.100 or root@bt:~#nmap -sC 192.168.1.100 |
this will give you more detailed information about particular IP-address like OS , netbios information , computer name and smb information.
12. Get the Scripting Help :-
| root@bt:~# nmap – -script-help discovery |
you can easily get the nmap scripting help with nmap – -script-help and put the group name.
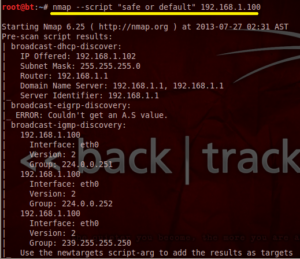
13. Run Safe or Default Script
| root@bt:~# nmap – -script “safe or default” 192.168.1.100 |
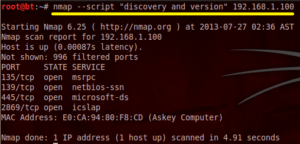
14. Find out Discovery and version Information
| root@bt:~# nmap – -script “discovery and version” 192.168.1.100 |
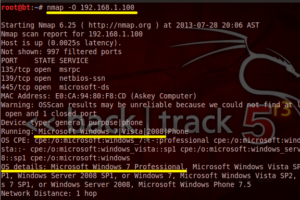
| root@bt:~# nmap –O <IP range> |
This command will do the Fingerprinting along with Port-scanning.
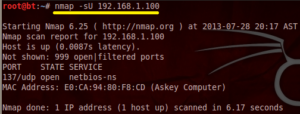
16. UDP Scanning with Nmap
| root@bt:~# nmap –sU <IP range> |
Also Check :-
Find Geolocation of an ip address or domain with Nmap
How to Find all domains on same IP address
Hope you like my post. Nmap – Free Security Scanner For Network Exploration and Hacking. Please Share with others.