What is Stateful Packet Inspection Firewall ?
“Stateful” basically means “remembers things that came before.” Something that is “stateful” knows about the current “state” of things — what’s going on at that moment, and what went on before that.
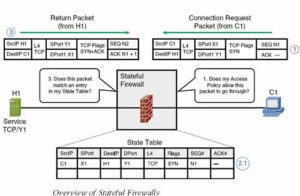
A “stateful” firewall knows not only about the packet it’s looking at, but also about packets that came before that one.
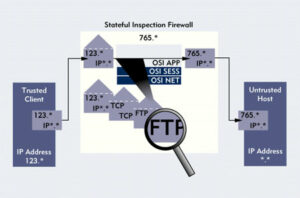
Stateful inspection is a firewall architecture that works at the network layer. Unlike static packet filtering, which examines a packet based on the information in its header, stateful inspection tracks each connection traversing all interfaces of the firewall and makes sure they are valid.
An example of a stateful firewall may examine not just the header information but also the contents of the packet up through the application layer in order to determine more about the packet than just information about its source and destination.
A stateful inspection firewall also monitors the state of the connection and compiles the information in a state table. Because of this, filtering decisions are based not only on administrator-defined rules (as in static packet filtering) but also on context that has been established by prior packets that have passed through the firewall.
As an added security measure against port scanning, stateful inspection firewalls close off ports until connection to the specific port is requested.
Windows Firewall is also doing the Stateful Packet Inspection. it,s making entery of all connection passing from your system. if you want to allow any connection you need to be create a policy.
But in the case of Network firewall, you need a ACL entry for allowing outside to inside connection.
In my future post. i will write more on cisco ASA and WatchGuard Firewall. If you want to read articles on Firewall. check my blog http://ccnpsecurity.blogspot.com .
Hope you like my post.What is Stateful Packet Inspection Firewall. Please Share with others.